Introduction to Ethical Hacking and its Importance
Ethical hacking refers to the practice of intentionally probing computer systems and networks with the goal of identifying security vulnerabilities. Unlike malicious hackers, ethical hackers operate with permission and are tasked with improving security measures. They play a vital role in the contemporary landscape of cybersecurity, ensuring that organizations remain protected against various threats.
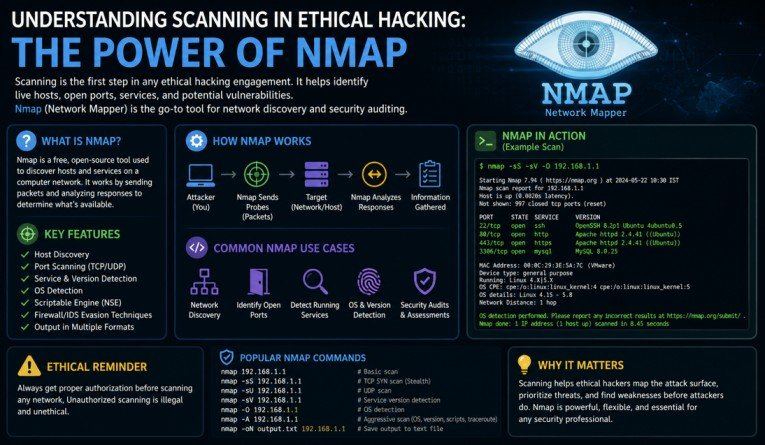
Cybersecurity is more crucial than ever in an age marked by rapid technological advancements, increasing connectivity, and the escalating sophistication of cyber threats. Ethical hacking contributes significantly to this field by employing various techniques, including scanning, which assists in revealing weaknesses before they can be exploited by unauthorized entities. By leveraging tools like Nmap, ethical hackers can perform network mapping and vulnerability assessments effectively.
Scanning, in this context, refers to the systematic examination of systems or networks to gather information, determine reachable hosts, open ports, and available services. This process allows ethical hackers to create a comprehensive profile of the target, which is critical for subsequent security measures. Ethical hackers utilize this insight to fortify the system, ensuring that vulnerabilities are remediated proactively.
Organizations are increasingly adopting ethical hacking as a preventive strategy. By hiring skilled professionals, they can cultivate a robust security posture that not only detects threats but also mitigates risks arising from potential cyber attacks. The effectiveness of ethical hacking is contingent upon a deep understanding of various scanning techniques and the ability to analyze the information gathered lucidly. Companies can ensure their sensitive data remains protected and that their security protocols adapt to emerging threats.
What is Scanning in Ethical Hacking?
Scanning is a crucial component of the ethical hacking process, enabling security professionals to assess the vulnerabilities present within a network or system. The primary purpose of scanning is to gather information about the target environment which can subsequently be utilized for identifying potential security weaknesses. This step is essential because, without comprehensive scanning, risk assessments may overlook critical vulnerabilities that could be exploited by malicious actors.
There are several types of scanning utilized in the realm of ethical hacking. One of the most common is network scanning, which involves identifying active devices on a network. During this process, ethical hackers can discern which devices are connected and their corresponding IP addresses. This technique not only aids in understanding the network topology, but it also facilitates the recognition of unauthorized devices that may pose security threats.
Another significant type is vulnerability scanning, through which tools identify known vulnerabilities present in systems or applications. This involves inspecting components versus a database of known vulnerabilities, which can be critical in preemptively addressing security flaws. Tools, such as Nmap, are frequently employed for this purpose, allowing ethical hackers to quickly discover potential weak points within the infrastructure.
Port scanning is yet another valuable technique that focuses on identifying open ports on networked devices. Each port serves as a gateway for communication, and by verifying the status of these ports, ethical hackers can determine which services are running and their potential vulnerabilities. Overall, scanning plays a pivotal role in ethical hacking, providing a foundation for subsequent analysis and remediation actions by identifying risks that need to be addressed by organizations like Cyber Yodha.
Types of Scanning Techniques
Ethical hacking heavily relies on various scanning techniques to identify vulnerabilities within a system or network. One of the most common methods is ICMP scanning, which uses the Internet Control Message Protocol to probe a target. This technique often targets the ICMP echo request messages that help in detecting live hosts on a network. By sending an echo request and awaiting a reply, ethical hackers can determine whether a device is active, thus providing valuable insights into the network landscape.
TCP scanning is another prevalent technique used to assess the security of a network. It operates by establishing a connection with the target host through the Transmission Control Protocol. This method helps in identifying open ports and services running on those ports, enabling security experts to evaluate potential vulnerabilities. TCP scanning can be executed in various ways: full connect scans, half-open scans, and fin scans among others. Each method varies in its stealth and effectiveness while obtaining crucial information.
Furthermore, UDP scanning is essential for detecting services on User Datagram Protocol ports. Unlike TCP, UDP is connectionless, making it challenging to ascertain whether a port is open or closed since it does not provide a direct acknowledgment. Ethical hackers typically employ this technique to scrutinize network applications and identify weaknesses that could be exploited in future attacks.
Lastly, application-level scanning allows ethical hackers to dive deeper into network applications, examining them for vulnerabilities such as SQL injection or cross-site scripting. This technique typically involves using specialized tools that interact with web applications to submit various requests. By analyzing the application’s responses, ethical hackers can glean insights into potential security flaws.
In conclusion, the scanning techniques employed in ethical hacking are foundational elements for system security analysis. They enable professionals to understand the landscape of a network and take appropriate measures to safeguard it effectively.
Why Nmap is the Best Tool for Network Scanning
Nmap, short for Network Mapper, has established itself as a premier tool for network scanning within the realm of ethical hacking. One of the key reasons for Nmap’s popularity among cybersecurity professionals is its remarkable flexibility. This open-source tool can be easily configured for a wide variety of scanning tasks, accommodating a broad spectrum of user needs. Whether one requires a simple ping scan to identify live hosts or a thorough scan targeting specific ports and services, Nmap provides the necessary functionalities to accomplish these objectives efficiently.
Another significant factor contributing to Nmap’s standing in the field of ethical hacking is its user-friendly interface coupled with powerful command-line options. The versatility of Nmap caters to both novice users and experienced hackers. For beginners, graphical user interfaces (GUIs) such as Zenmap can simplify the scanning process, while seasoned ethical hackers can leverage Nmap’s extensive command-line options for more intricate and variable scanning scenarios. This dual capability ensures that users from varying backgrounds can benefit from Nmap’s features.
Furthermore, Nmap’s extensive capabilities in detecting live hosts and open ports play a vital role in its recommendation as the go-to tool for network scanning. With its ability to identify services running on devices and to generate detailed information about operating systems, Nmap can facilitate comprehensive assessments of network security. Ethical hackers utilize this data to uncover potential vulnerabilities, thereby enhancing the overall security posture of networks. This dynamic ability to provide thorough insights into network configurations gives Nmap an edge over its competitors in the ethical hacking domain.
Key Features of Nmap
Nmap, short for Network Mapper, is a powerful tool widely utilized in the realm of ethical hacking for its impressive features that aid in network scanning and exploration. One of the key distinguishing characteristics of Nmap is its robust scripting engine, known as Nmap Scripting Engine (NSE). This allows users to create scripts that automate a multitude of tasks, ranging from simple service discovery to advanced vulnerability detection. By leveraging NSE, ethical hackers can customize their scanning processes tailored to specific scenarios, significantly enhancing their productivity.
Another notable feature is Nmap’s extensive support for various protocols, including TCP, UDP, and SCTP, among others. This flexibility enables comprehensive scanning capabilities to identify live hosts, open ports, and services running on those ports. The ability to utilize different scanning techniques, such as SYN Stealth scans, UDP scans, and version detection, empowers cybersecurity professionals to choose appropriate methods depending on their objectives and the network’s characteristics.
In addition to its scanning prowess, Nmap is renowned for its advanced network exploration features. It is capable of generating detailed network topology maps, providing ethical hackers with visual insights into the structure and components of the network. Furthermore, Nmap offers operating system detection and service version detection, allowing users to ascertain critical information about the devices and applications present in the environment. Such capabilities are indispensable for security assessments, as they facilitate an informed approach to identifying and mitigating potential vulnerabilities.
Ultimately, these key features of Nmap not only streamline the scanning process but also empower ethical hackers, such as those at Cyber Yodha, to conduct thorough assessments that can preemptively identify and address security threats, making it an invaluable asset in the field of cybersecurity.
Advantages of Using Nmap in Ethical Hacking
Nmap, short for Network Mapper, is a powerful tool widely recognized in the field of ethical hacking for its precise capabilities in network scanning. One of the primary advantages of using Nmap is its remarkable accuracy in mapping extensive networks. This proficiency allows ethical hackers to visualize their target networks comprehensively, identifying active devices, subnets, and the overall network topology. The detailed information generated can facilitate further analysis and planning for subsequent penetration testing methodologies.
Another significant benefit of Nmap is its ability to identify open ports and the services running on those ports. This feature enables ethical hackers to assess the security posture of a system by highlighting vulnerable services. By recognizing these points of entry, ethical hackers can prioritize their responses and remedial actions accordingly. Additionally, Nmap can employ various scanning techniques to detect vulnerabilities associated with those services, providing insights into potential exploits that could be leveraged by malicious actors.
A third advantage of using Nmap is its robust community support, which is vital for both novice and experienced ethical hackers alike. The Nmap Community provides extensive documentation, tutorials, and user forums that enhance the learning curve and troubleshooting processes. This support network facilitates continuous knowledge sharing among security professionals, empowering them to share successful scanning techniques, vulnerability discovery, and effective mitigation strategies. The ongoing updates and enhancements to Nmap ensure that ethical hackers are equipped with the latest tools and features necessary for effective scanning in the ever-evolving landscape of cyber threats.
Real-World Applications of Nmap in Security Assessments
Nmap, a versatile and widely used network scanning tool in ethical hacking, plays a significant role in aiding organizations to assess their security postures. Its applicability spans various real-world scenarios where effective scanning is crucial for maintaining robust cybersecurity defenses.
One of the most notable uses of Nmap is during penetration testing engagements. Ethical hackers utilize Nmap to discover vulnerabilities within an organization’s network infrastructure. By executing different scanning techniques, such as TCP connect scans and SYN scans, security professionals can identify open ports and services running on these ports, which may potentially harbor security weaknesses. This information is critical for devising targeted attack simulations and uncovering possible entry points for malicious actors.
Additionally, Nmap is instrumental in network troubleshooting for organizations that seek to maintain optimal performance. Network administrators can utilize Nmap to map out the network topology, ensuring that all devices are correctly configured and operational. By identifying rogue devices or unauthorized access points that may pose security threats, administrators can take necessary remediation steps to protect sensitive data and maintain compliance with cybersecurity standards.
Moreover, Nmap’s scripting engine allows security teams to leverage powerful scripts to automate various scanning tasks, enhancing efficiency and accuracy during assessments. For instance, organizations might apply pre-built scripts to detect vulnerabilities such as SQL injection or misconfigurations within their systems. This automation aspect greatly streamlines the process of conducting regular security assessments, thereby promoting proactive defense measures.
In conclusion, Nmap serves as an invaluable tool in the realm of ethical hacking and security assessments, offering organizations the ability to perform thorough scanning exercises. By utilizing Nmap for penetration testing and network troubleshooting, companies can more effectively shield their networks from potential threats and enhance their overall security posture.
Common Challenges and Limitations of Network Scanning
Network scanning, while a powerful tool in ethical hacking, does come with its own set of challenges and limitations that practitioners must navigate to maximize effectiveness and minimize risks. One notable challenge encountered during the scanning process is the occurrence of false positives. False positives emerge when scanning tools like Nmap report active hosts or open ports that are, in fact, not there or are falsely identified. This not only leads to wasted resources but also could mislead ethical hackers into making incorrect assessments about a network’s security posture.
Another significant limitation arises from network segmentation. Organizations often implement strategies to segment their networks for enhanced security. Each segment may be governed by distinct access controls and firewalls, which can impede the efficacy of scanning efforts. Ethical hackers may find themselves unable to engage with certain segments or discover vulnerabilities simply because their scanning tools cannot traverse the complex pathways formed by segmentation. Consequently, this can leave blind spots that remain unassessed.
Furthermore, there exists the potential for the detection of scanning activities by intrusion detection systems (IDS) or intrusion prevention systems (IPS). Particularly with aggressive scanning methods, there is a risk that alerts will trigger, resulting in unwanted scrutiny from network administrators. This not only complicates the ethical hacker’s role but might also lead to legal implications, which is why recognizing the scope of the engagement is vital.
Together, these factors underscore the necessity for ethical hackers to adopt a strategic approach, utilizing Nmap and other scanning tools judiciously while remaining aware of the inherent limitations they present. Ultimately, addressing these challenges proactively can enhance the overall effectiveness of security assessments.
Conclusion and Best Practices in Scanning
In the realm of ethical hacking, effective scanning plays a pivotal role in identifying vulnerabilities within a network. One of the most powerful tools available for this purpose is Nmap. Known for its versatility and robust feature set, Nmap enables ethical hackers to perform comprehensive scans that reveal security flaws and misconfigurations. Through methods such as port scanning, service enumeration, and OS detection, Nmap provides critical insights into network security, thereby facilitating proactive measures for protection.
As we have explored, scanning forms the foundation of a successful ethical hacking strategy. The ability to accurately assess a network’s security posture directly impacts the effectiveness of subsequent steps in the hacking process, such as exploitation and remediation. Using Nmap, ethical hackers can not only discover open ports and running services but also gather valuable intelligence about potential attack vectors. This intelligence is essential for developing a thorough understanding of risks and mitigating vulnerabilities.
However, to maximize the effectiveness of scanning, it is imperative for ethical hackers to follow best practices. First and foremost, always obtain necessary permissions before conducting any scans, as unauthorized scanning can lead to legal ramifications. Additionally, familiarize yourself with the target network’s policies and structure to perform more tailored scans. Make use of Nmap’s various scanning options to adjust the intensity and specificity of your searches according to the environment. Furthermore, analyzing the results in a structured manner and prioritizing vulnerabilities based on risk can significantly enhance your security posture.
In conclusion, the importance of scanning in ethical hacking cannot be overstated, especially with powerful tools like Nmap at one’s disposal. By following best practices and emphasizing thorough analysis, ethical hackers can significantly contribute to the safeguarding of digital environments against malicious threats, as exemplified by resources such as Cyber Yodha that offer guidance and expertise in this domain.