Introduction to Android Hacking
Android hacking refers to the practice of exploiting vulnerabilities within the Android operating system to gain unauthorized access to devices or applications. This crucial field is significant due to the widespread use of Android mobile devices throughout the world, making them potential targets for malicious attacks. As millions of users rely on Android for personal and professional tasks, mastering Android hacking techniques can play a vital role in enhancing security measures and protecting sensitive data.
Understanding the structure of the Android OS is paramount for anyone interested in this domain. Android is based on a modified version of the Linux kernel and includes a rich application framework that facilitates app development. Proficiency in this operating system allows hackers—both ethical and malicious—to identify weaknesses that may be exploited. Ethical hackers, in particular, utilize their skills to discover vulnerabilities before they can be breached by nefarious actors, ultimately contributing to the safety of users and organizations.
Various hacking techniques are applicable within the Android ecosystem, each differing in complexity, purpose, and ethical implications. Techniques can range from penetration testing to reverse engineering of applications to understand how they operate. The significant aspect of this discipline lies in adhering to ethical standards. Ethical hacking is characterized by explicit permission to assess systems for vulnerabilities, while malicious hacking typically involves illegal access to data and devices without consent, leading to severe legal ramifications.
In pursuit of mastering Android hacking, individuals must navigate a landscape that encompasses a variety of tools, programming languages, and methodologies. Familiarity with Java and Android Studio is crucial, as they form the foundation of Android application development and are integral to understanding potential security flaws. As interest in Android hacking continues to grow, so does the need for responsible, knowledgeable practitioners who prioritize security and ethics in this rapidly evolving technological environment.
Understanding Android Architecture
The Android operating system is a complex ecosystem, rooted in various components that serve distinct functions yet work harmoniously to create a cohesive platform. At its core lies the Linux kernel, which provides a robust base for Android by managing hardware resources and facilitating communication between the device’s hardware and software. This kernel is fundamental in orchestrating core features such as memory management, process management, and security.
Building upon the Linux kernel is the Android Runtime (ART), which serves as an essential environment for executing Android applications. ART utilizes an Ahead-of-Time (AOT) compilation method to convert applications into native machine code upon installation, enhancing performance and reducing runtime overhead. This process allows Android applications to run more efficiently compared to the older Dalvik runtime, which employed Just-in-Time (JIT) compilation.
The Android application framework sits atop the Android Runtime and provides a higher-level API that developers can utilize to create applications. It comprises key services such as activity management, content providers, and resource management. Through this framework, developers gain access to system tools, enabling them to create applications that can interact with the device hardware, user interface, and other applications seamlessly. The framework’s components communicate through standardized methods, ensuring that applications can perform as intended, leveraging the underlying architecture effectively.
Interactions among these components are vital for a comprehensive understanding of Android architecture. The layering of the Linux kernel, Android Runtime, and Application Framework operates in tandem, allowing for optimal performance and security features vital in today’s mobile environment. Such knowledge is especially crucial for those interested in Android hacking, as understanding the architecture equips hackers with insights into how to exploit vulnerabilities and enhance their skills.
Why Java is Vital for Android Development
Java serves as the cornerstone programming language for Android development, primarily due to its versatility and robustness. As a high-level programming language, Java provides several features that are essential for building efficient and effective Android applications. Its object-oriented nature facilitates a modular approach to development, allowing developers to create reusable code components, which can be particularly beneficial when addressing the often complex requirements of Android apps.
One significant advantage of Java is its platform independence. Java’s Write Once, Run Anywhere (WORA) capability enables developers to write an application once and execute it on any device that supports the Java Virtual Machine (JVM). This feature aligns perfectly with Android’s architecture, where applications need to function seamlessly across various device types and screen sizes. By understanding Java, developers can ensure that their applications maintain performance and functionality across the diverse Android ecosystem.
Additionally, Java encompasses a vast array of libraries and frameworks that simplify Android development processes. Popular frameworks such as Spring and Hibernate offer pre-built solutions for common programming tasks, further boosting productivity. Moreover, the extensive Java community provides a wealth of resources, documentation, and support systems, making it easier for novice and experienced developers alike to solve problems and enhance their skills.
Mastering Java, therefore, is crucial for anyone aspiring to delve into Android hacking. Understanding how to navigate the intricacies of Java allows developers to not only create complex applications but also secure them against potential threats. Java’s features empower developers to implement strong security measures, incorporate encryption, and understand vulnerabilities in their code, all of which are essential elements in the landscape of Android security.
Getting Started with Android Studio
Android Studio is the official Integrated Development Environment (IDE) for Android application development, providing developers with the tools needed to create sophisticated apps. Designed specifically for Android development, it offers excellent features that streamline the development process. First, you will need to download and install Android Studio, which is available for Windows, macOS, and Linux. The installation is straightforward; simply follow the prompts provided by the setup wizard to install the necessary components.
Once you have successfully installed Android Studio, you can start a new project by selecting the “Start a new Android Studio project” option. The IDE allows you to choose different project templates, including options for empty activity, basic activity, or a full navigation drawer template. This flexibility makes it easier for beginners to select a starting point that suits their individual needs. For new users, it is advisable to start with the “Empty Activity” template, as this provides a clean slate to explore the fundamentals of app development.
Android Studio is integrated with tools that are essential for app development, such as a code editor, debugging tools, and an emulator for testing. The code editor features syntax highlighting, code completion, and refactoring capabilities, all of which enhance the coding experience. The built-in emulator allows developers to run their applications on virtual devices, facilitating testing without needing physical hardware. Additionally, Android Studio supports Git version control and provides tools for collaboration, making it ideal for team projects.
For newcomers, familiarizing oneself with the user interface and navigation of Android Studio is crucial. The IDE’s layout comprises a project view, editor window, and various tool windows for managing resources and dependencies. Understanding these elements will significantly assist in building and managing Android applications efficiently. By leveraging the robust features of Android Studio, developers can effectively translate their ideas into functional applications.
Building Your First Android Application
Creating your first Android application is an exciting and rewarding experience, laying the groundwork for your journey in Android development. To begin, ensure you have Android Studio installed on your computer. This integrated development environment (IDE) provides a comprehensive suite of tools necessary for building applications. Once you have Android Studio ready, launch the application and start a new project by selecting ‘Start a new Android Studio project’ from the welcome screen.
During project setup, you will need to define the project name, package name, and choose a project template. For beginners, the ‘Empty Activity’ template is recommended, as it creates a simple framework to build upon. After configuring these initial settings, Android Studio will generate the basic files needed to start your application.
Next, focus on understanding the concept of activities and layouts. An activity represents a single screen in your application, while layouts define the user interface elements visible on that screen. Navigate to the ‘res/layout’ directory and open the ‘activity_main.xml’ file. Here, you can use the drag-and-drop interface to add user interface components such as buttons, text fields, and images. Adjust the properties of these components through the attributes panel to customize their appearance and functionality.
Once you have designed your layout, it is essential to link it to your Java code. Open the ‘MainActivity.java’ file associated with the activity you created. This is where you will implement the logic for your application. For instance, you can define what happens when a user clicks a button or enters text in a field. By writing simple Java code within various lifecycle methods like ‘onCreate()’, you can manage the interplay between UI components and application behavior.
This fundamental experience of creating an Android application equips you with the skills necessary to delve deeper into Android development. As you progress, you will encounter more complex features and concepts, enhancing your expertise in this exciting field.
Common Android Security Vulnerabilities
As Android continues to dominate the mobile operating system market, understanding the common security vulnerabilities that affect Android applications and the platform itself becomes crucial. One prevalent issue is insecure data storage. Many applications fail to adequately protect sensitive user data, such as passwords and personal information, leading to unauthorized access. Developers often store this information in easily accessible locations, such as in application folders or shared preferences, without any encryption, making it an easy target for attackers.
Another significant vulnerability lies in improper authentication mechanisms. Many Android applications do not implement robust user authentication methods, which can result in unauthorized access and exploitation of user accounts. Weak or fixed passwords, lack of multi-factor authentication, or failure to properly validate user input can open the door to a variety of attacks, including credential stuffing and brute force attacks. Thus, developers must prioritize the implementation of secure authentication processes.
Additionally, code vulnerabilities remain a persistent issue in many Android applications. Flaws in the code, such as buffer overflows, injection attacks, or insecure API calls, can be exploited by malicious actors to gain control of the application or data. Furthermore, mobile applications often rely on third-party libraries, which can introduce additional vulnerabilities if not updated regularly or if they contain undisclosed weaknesses. Developers are advised to conduct regular security assessments and code reviews to identify and remediate these vulnerabilities.
By raising awareness of these common Android security vulnerabilities, developers can take proactive steps to protect their applications from potential threats. Addressing issues such as insecure data storage, improper authentication, and code vulnerabilities is essential to ensuring the safety and integrity of user data and maintaining the trust of application users.
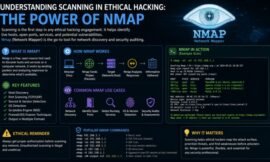
Tools and Techniques for Android Hacking
In the evolving landscape of cybersecurity, it is imperative for individuals engaged in Android hacking to arm themselves with the right tools and methodologies. These tools can significantly enhance the process of assessing Android applications and their security vulnerabilities. A vast array of penetration testing tools have been developed specifically for this purpose, allowing security professionals to conduct thorough analyses of mobile applications.
One notable tool in this realm is Burp Suite, widely recognized for its ability to intercept and modify network traffic. Security experts employ this tool to identify vulnerabilities within mobile applications by examining the requests and responses exchanged between the app and server. Another essential tool is MobSF (Mobile Security Framework), a powerful open-source mobile application security testing tool that automates the assessment process. It provides features for static and dynamic analysis, ensuring comprehensive coverage of potential weak points.
In addition to these tools, the Android Debug Bridge (ADB) plays a crucial role in Android hacking. ADB facilitates communication with an Android device, allowing hackers to execute commands directly, which can include installing and debugging apps. This method of testing is essential for developing a secure application, as it enables the tester to observe real-time interactions and potential vulnerabilities.
Furthermore, methodologies such as OWASP Mobile Security Testing Guide provide a structured framework for conducting security assessments on mobile applications. This guide emphasizes ethical practices, asserting that hacking should only be performed with applicable permissions and under legal boundaries. Responsible usage of these tools and techniques ensures the advancement of security protocols while safeguarding user data.
Ethical Considerations and Legal Aspects
As the domain of Android hacking expands, it is imperative to adhere to ethical considerations and legal aspects associated with this practice. Ethical hacking, often referred to as penetration testing, involves the authorized probing of digital systems, applications, and networks to uncover vulnerabilities that might be exploited by malicious actors. Practicing ethical hacking requires individuals to operate within a framework of legally sanctioned actions, ensuring that their activities are not only lawful but also contribute positively to the field of cybersecurity.
Individuals aspiring to be involved in Android hacking must be acutely aware of the laws governing computer security in their respective regions. Unauthorized access to devices is illegal and can lead to severe penalties, including fines and imprisonment. Thus, acquiring explicit permission from device owners or organizations before initiating any testing or hacking attempts is crucial. Moreover, it is advisable to engage in ethical hacking training or certification programs, as these resources provide essential insights into legal norms and ethical standards that govern the profession.
Furthermore, an ethical hacker should be motivated by a sense of integrity and responsibility, always prioritizing the security and privacy of users. This encompasses respecting the confidentiality of sensitive data and reporting vulnerabilities to the appropriate stakeholders rather than exploiting them. Engaging in discussions with peers and participating in communities dedicated to ethical hacking can foster a culture of collaboration and shared knowledge, reinforcing the necessity of ethical standards in the hacking arena. By embracing these principles, individuals can not only improve their skills in Android hacking but also contribute to a safer digital environment.
Resources for Continued Learning
For individuals looking to deepen their understanding and skills in Android hacking, a variety of resources are available that cater to different learning styles and preferences. The exploration of these resources can not only enhance technical proficiency but also foster a vibrant community of practice.
Online courses are an excellent starting point. Platforms like Coursera, edX, and Udemy offer a range of courses focused on Android development and cybersecurity principles. Courses such as “Android App Development for Beginners” and “Ethical Hacking: Introduction to Hacking on Android” can be particularly beneficial. Most of these courses provide hands-on projects that facilitate the application of theoretical concepts in practice.
Books also serve as a valuable resource for learning. Titles such as “Android Hacker’s Handbook” and “Java for Android” provide in-depth knowledge about the Android operating system’s architecture and the key components necessary for Android hacking. These books often include practical examples and code snippets to illustrate concepts effectively.
Another essential avenue for consistent learning is through online forums and communities. Websites like Stack Overflow, Reddit, and specialized forums such as XDA Developers are great places to engage with experienced hackers and developers. Participating in discussions can provide insights into the latest tools, techniques, and trends in Android hacking.
Furthermore, attending workshops and webinars can offer a hands-on experience, allowing learners to interact with experts in the field. Networking during these events can open doors to mentorship opportunities and collaborations.
In summary, by leveraging online courses, books, forums, and community interactions, aspiring Android hackers can cultivate a robust understanding of both the practical and theoretical aspects of Android hacking. These resources not only enhance individual skills but also contribute to a broader understanding of the cybersecurity landscape surrounding Android devices.