Introduction to Information Gathering
Information gathering is a crucial first step in the realms of cyber security and penetration testing. It refers to the systematic process of collecting and analyzing information about a target system, network, or organization. This critical phase enables ethical hackers to identify potential vulnerabilities and gather intelligence that informs subsequent testing strategies. In today’s digital landscape, the ability to efficiently gather pertinent information is paramount, as it empowers security professionals to preemptively address threats before they manifest.
The importance of information gathering cannot be overstated. It serves not only as a foundation for penetration testing but also as a component of broader security assessments. By meticulously collecting details such as domain names, IP addresses, and network configurations, penetration testers can construct a comprehensive attack surface map. This process facilitates risk management, ensuring that security measures are tailored effectively to the specific threats that may be faced.
Tools play an integral role in aiding the information gathering process. With the advent of sophisticated software and utilities, the analysis has become less cumbersome and more effective. Kali Linux, a widely recognized operating system within the ethical hacking community, offers a variety of tools designed specifically for information gathering. These tools automate repetitive tasks, streamline data collection, and enhance the accuracy of the findings. Understanding how to leverage these tools effectively is paramount for ethical hackers aiming to refine their techniques and strategies.
As we delve deeper into this important aspect of cyber security, we will explore specific tools available in Kali Linux that excel in the information gathering phase, emphasizing their features and best applications. The right toolkit can significantly boost the efficacy of an ethical hacker’s efforts, making it vital to stay informed about the latest technologies and methodologies.
Overview of Kali Linux for Information Gathering
Kali Linux stands out as a premier penetration testing distribution designed specifically for security assessment and ethical hacking. Its development is managed by Offensive Security and is based on Debian. This specialized Linux distribution is equipped with a wide array of tools that facilitate information gathering, vulnerability assessment, and exploitation—all integral components in the realm of cyber security.
The significance of Kali Linux in the field of ethical hacking cannot be overstated. It not only serves as an essential platform for conducting routine security audits but also acts as a comprehensive repository for experienced professionals and newcomers alike. With tools that range from network analysis utilities to advanced digital forensics, Kali Linux supports a vast spectrum of tasks crucial for ethical hackers. Each tool is tailored to gather and analyze data, enabling security practitioners to identify vulnerabilities within systems.
One of Kali Linux’s defining features is its adaptability. Users can customize their environments and choose specific tools that cater to their information gathering needs. Furthermore, Kali is frequently updated, ensuring that it incorporates the latest security technologies and methodologies. This constant evolution is vital in a field where cyber threats are perpetually advancing.
Additionally, Kali Linux is supported by a robust community of users and developers, providing a wealth of shared knowledge, tutorials, and forums. This vibrant ecosystem enhances the resources available for anyone looking to deepen their understanding of ethical hacking and cyber security practices. Overall, Kali Linux remains an indispensable resource for anyone involved in information gathering, making it a favored choice for ethical hackers worldwide.
Key Features to Look for in Information Gathering Tools
When selecting information gathering tools within Kali Linux, various features are critical to ensure effectiveness in tasks performed by ethical hackers and cybersecurity professionals. First and foremost, ease of use is paramount. Tools that provide a user-friendly interface enable both novice and experienced users to efficiently navigate the functionalities without extensive prior knowledge. A well-designed user interface reduces the learning curve and increases productivity, allowing professionals to focus on gathering pertinent data instead of grappling with complex commands.
Versatility is another essential feature. Information gathering tools should cater to multiple purposes, whether it is conducting reconnaissance, identifying vulnerabilities, or collecting general data about target systems. A versatile tool suite enables ethical hackers to adapt their approach based on the scenario, facilitating a more comprehensive cybersecurity assessment.
Compatibility with various systems enhances the effectiveness of information gathering tools. Given that attackers may use a range of technologies, the ability to operate across different operating systems and environments is a noteworthy advantage. Tools that are flexible in deployment can seamlessly integrate into various workflows and provide holistic information gathering capabilities.
Moreover, the effectiveness in data collection is an indispensable characteristic. The accuracy and reliability of gathered information can significantly influence the outcome of ethical hacking endeavors. Tools should demonstrate a proven ability to extract insightful data efficiently, as this directly correlates with the quality of information that cybersecurity assessors will later analyze.
Lastly, community support is invaluable. A robust user community can assist in resolving issues, sharing software updates, and enhancing tool functionality. When faced with challenges, having access to a knowledgeable community enhances the overall experience and effectiveness of the information gathering process.
Top Information Gathering Tools in Kali Linux
Kali Linux is a renowned distribution designed for penetration tests and security assessments, and it incorporates a variety of sophisticated tools for information gathering. In 2026, several tools stand out as essential for ethical hackers aiming to enhance their cyber security efforts.
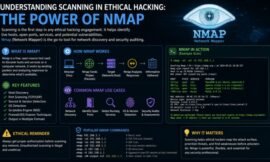
One of the most popular tools within Kali Linux is Nmap. This network scanning tool allows ethical hackers to discover hosts and services on a network, thereby collecting valuable data. Its ability to perform host discovery, port scanning, and service enumeration makes it indispensable for security professionals looking to gather comprehensive network information.
Another significant tool is Maltego, which excels in information collection and visualization. Maltego provides a powerful platform for gathering and correlating data from various online sources. By creating graphical representations of connections between entities, ethical hackers can derive insights that are critical for understanding the landscape of potential security threats.
Recon-ng is also noteworthy, as it offers a web reconnaissance framework designed for information gathering. This tool comes equipped with a range of modules that facilitate data collection from numerous sources such as APIs and web scrapers. Its ease of use and powerful reporting features make it suitable for both novices and seasoned security experts.
Finally, TheHarvester provides a concise and effective way to gather email addresses and subdomain names. This tool fetches data from search engines and public sources to compile valuable information, making it a must-have for any ethical hacker’s toolkit.
Utilizing these tools effectively can significantly enhance an ethical hacker’s capabilities in cyber security, emphasizing the importance of thorough information gathering in identifying and mitigating potential vulnerabilities.
Comparative Analysis of Information Gathering Tools
The landscape of information gathering tools in Kali Linux encompasses a diverse range of utilities, each designed to serve particular purposes and scenarios. By analyzing the strengths and weaknesses of these tools, ethical hackers can make informed decisions based on their specific needs in cyber security.
Starting with Nmap, this tool excels in network mapping and security auditing. Its ability to identify open ports and services makes it invaluable for initial reconnaissance. However, while Nmap is powerful, it might not provide detailed vulnerability assessments, which can necessitate the use of additional tools alongside it.
Maltego stands out for its visually intuitive interface and its capability to gather information from various sources, allowing users to perform deep investigative analysis. Its ability to depict relationships between different entities is highly beneficial, yet it can be overwhelming for beginners and may require a substantial learning curve.
theHarvester specializes in gathering email addresses and subdomains, pulling valuable data from different public sources. It is particularly effective in social engineering scenarios. However, its focus on specifics means it may lack the broad application that other tools provide.
Another notable tool is Recon-ng, which integrates different modules to streamline the information gathering process across multiple platforms. Its versatility allows ethical hackers to customize their approach, although users must be familiar with the command-line interface to harness its full potential effectively.
Each of these tools offers unique advantages and drawbacks, so ethical hackers must consider the task at hand. Factors such as ease of use, required information type, and depth of analysis will guide tool selection based on their specific information gathering needs.
Case Studies: Successful Information Gathering Using Kali Linux Tools
Information gathering is a critical phase in the penetration testing process, and various tools available in Kali Linux have proven effective for ethical hackers in real-world scenarios. This section details notable cases where specific tools facilitated successful information gathering, highlighting their practical applications in enhancing cyber security.
One exemplifying scenario involves the use of Recon-ng, a powerful recon tool in Kali Linux, during a penetration test for a large financial institution. The ethical hacker employed Recon-ng to perform an automated analysis of the target’s domain and associated assets. As a result, the tool uncovered subdomains, open ports, and even exposed sensitive information linked to employees, enabling the security team to patch vulnerabilities that could have been exploited.
Another case study highlights the use of Nmap for information gathering on a healthcare service provider. The ethical hacker was tasked with identifying potential entry points for an attack. Utilizing Nmap, they scanned the network to determine active devices and services running on various ports. This information proved instrumental in determining security levels and the existence of outdated software, which ultimately led to successful remediation and fortification of the network’s defenses.
Additionally, a cybersecurity firm conducted a red team exercise utilizing Maltego to gather intelligence on an e-commerce platform. By incorporating various data sources, Maltego allowed the team to visualize relationships among entities, leading to the discovery of potential phishing targets. This information gathering process was pivotal, as it revealed actionable insights that enhanced the client’s security awareness and training programs.
These case studies underscore the importance of effective information gathering tools in the realm of cyber security. As organizations face increasingly sophisticated threats, leveraging the capabilities of Kali Linux tools enables ethical hackers to identify weaknesses proactively, thereby strengthening overall security posture.
Community Contributions and Development of Tools
The open-source community plays a pivotal role in the evolution and enhancement of information gathering tools within Kali Linux, a distribution tailored for penetration testing and ethical hacking. This collaborative environment encourages developers and users alike to contribute their knowledge, code, and experience, facilitating a continuous improvement cycle for various cyber security tools.
Forums, such as Kali’s official forum and cybersecurity-focused platforms, serve as vital resources for information sharing. Here, users can discuss techniques, report bugs, and provide insights into the effective use of tools. These discussions help new and experienced ethical hackers understand the nuances of information gathering, from utilizing basic command-line tools to deploying advanced applications that aggregate data more efficiently.
Additionally, repositories like GitHub host a plethora of projects developed by both professionals and hobbyists. Through version control, contributors can refine existing tools or create innovative solutions to emerging challenges in cyber security. Many tools can be downloaded and integrated directly into Kali Linux, empowering users with the latest functionalities as they are developed.
Moreover, online tutorials and workshops offer further assistance, enabling individuals to enhance their skill sets systematically. These educational resources are crucial for those looking to deepen their understanding of information gathering methodologies. They provide step-by-step guidelines on the deployment and customization of various tools, ensuring that users can maximize their efficiency while working on penetration testing assignments.
Ultimately, the synergy created through community contributions significantly enriches the information gathering toolkit available in Kali Linux, allowing ethical hackers to stay abreast of industry trends and best practices in cyber security.
Future Trends in Information Gathering Technologies
The landscape of information gathering technologies is evolving rapidly, influenced by advancements in cyber security and the increasing sophistication of threats faced by organizations. As we look towards 2026 and beyond, several trends emerge that are likely to reshape the tools and strategies used by ethical hackers and cyber security professionals.
One significant trend is the enhancement of automation in information gathering processes. Automated tools are being developed to streamline the collection and analysis of data, significantly reducing the time required for reconnaissance tasks. These developments will not only improve efficiency but also minimize the potential for human error during data collection. Expect to see an integration of artificial intelligence (AI) and machine learning (ML) capabilities in such tools, empowering ethical hackers to gather and analyze vast amounts of information quickly.
Moreover, we anticipate the rise of integrated platforms that combine various information gathering tools. This integration will facilitate a more holistic approach to cyber security, enabling security professionals to utilize multiple sources and methods within a single framework. Such platforms will enhance the synergy between information gathering tools and other security solutions, providing deeper insights and actionable intelligence.
Additionally, privacy concerns and compliance regulations will influence the evolution of information gathering technologies. As data protection becomes increasingly crucial, tools that emphasize ethical practices and adherence to legal standards will become paramount. Cyber security practitioners will need to balance their information gathering efforts with ethical considerations to maintain trust and legitimacy.
In conclusion, the future of information gathering technologies is poised to witness significant advancements in automation, integration, and ethical compliance. As these trends develop, they will shape the methodologies of ethical hackers and enhance the overall effectiveness of cyber security strategies, ensuring organizations remain vigilant against emerging threats.
Conclusion and Recommendations
As we have explored throughout this blog post, information gathering is a crucial aspect of the cyber security landscape. An ethical hacker must utilize a variety of tools available in Kali Linux to efficiently gather the necessary information that can aid in identifying vulnerabilities and potential attack surfaces. The tools discussed, such as Nmap, Maltego, and theharvester, exemplify the diversity of techniques available for different information gathering tasks.
In choosing the right tools, it is vital to assess your specific requirements, including the type of information needed and the environment you are working within. For instance, Nmap is excellent for network mapping and assessments, while Maltego offers powerful data visualization options that can help in mapping complex relationships. Similarly, theharvester can be particularly effective for reconnaissance on email addresses and domain names. Each tool serves a distinct purpose, and thus the selection should align with the intended objectives.
Furthermore, it is advisable to stay updated on new developments within the information gathering landscape. The field of cyber security is constantly evolving, and keeping abreast of the latest tools, features, and techniques is imperative for any ethical hacker seeking to enhance their skills. Engaging in online forums, following industry leaders, and participating in relevant trainings can provide valuable insights and updates.
In conclusion, effective information gathering for an ethical hacker goes beyond merely selecting tools; it requires an understanding of the context of their use and staying informed about innovations in the field. By choosing the right tools and continually educating oneself, individuals can better position themselves in the ever-changing domain of cyber security.